Originally Published October 6, 2016. Updated For Today’s Threat Landscape!
We first wrote this blog post back in 2016 – The old line, the more things change, the more they stay the same still works – every year, we still encounter the same misunderstanding:
“We already did an external vulnerability scan. That’s the same thing as a penetration test, right?”
Not even close.
Although not as common as the internal penetration test vs. internal vulnerability assessment misconception, we do often hear the same misconceptions about external tests from many of the highly regulated organizations we work with. Often, institutions believe they’ve tested their external exposure — only to discover later that they received little more than an automated scan with no validation, no exploitation, and no insight into real-world attack paths.
Let’s clear this up.
External Vulnerability Assessment: What It Is (and Isn’t)
An External Vulnerability Assessment is primarily an automated, point-in-time scan of approved internet-facing systems using commercial tools such as Nessus, Qualys, or similar platforms.
These tools are valuable — but limited.
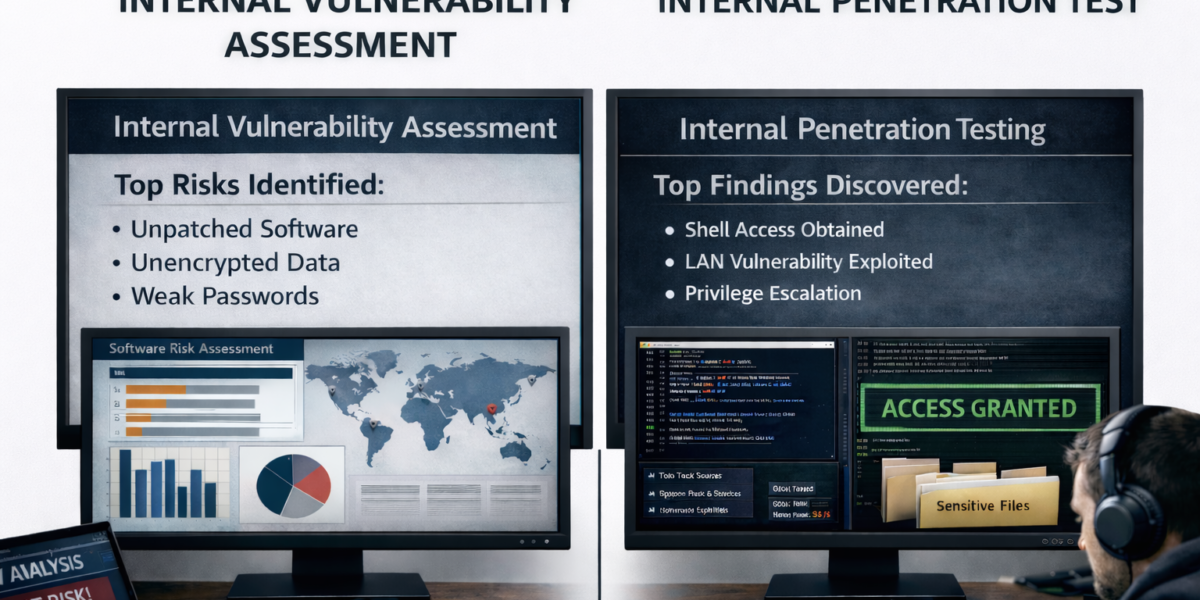
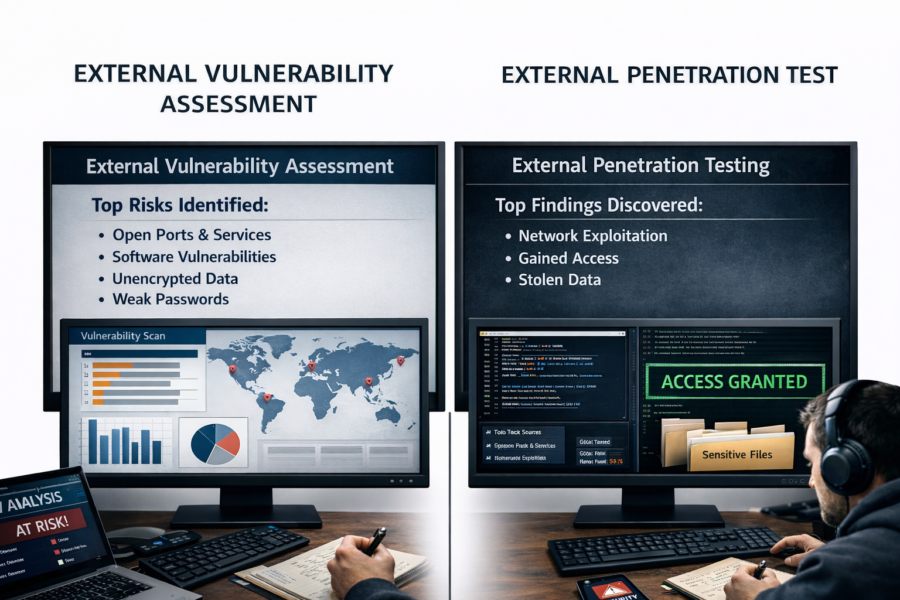
A typical external vulnerability assessment delivers:
- A high-level executive summary of detected vulnerabilities
- Generic remediation guidance aligned to CVEs
- Raw scanner output and severity rankings
For some organizations, this may be sufficient as a baseline hygiene check or regulatory checkbox. However it leaves critical questions unanswered — especially in today’s threat landscape.
The Gaps That Matter in 2026
An automated scan does not tell you:
- Whether attackers are already using stolen credentials to bypass perimeter defenses
- Whether identified vulnerabilities are actually exploitable in your environment
- How Identity, VPN, or cloud misconfigurations factor into risk
- How individual issues combine into real attack paths
Most importantly:
Vulnerability scanners do not think like attackers.
And attackers are no longer relying on noisy exploits — they’re logging in.
External Penetration Testing: How Real Attacks Actually Happen
An External Penetration Test is a human-driven adversary simulation designed to answer one question:
“If someone targets us today, how do they actually get in?”
Like all external testing, penetration tests require a clearly defined scope – including approved IPs, domains and testing windows. Rebyc Security strictly adheres to that scope.
Reconnaissance & Intelligence Gathering
Attackers don’t start with IPs — they start with information.
During this phase, testing includes reconnaissance of publicly discoverable information, such as:
- Externally exposed infrastructure and cloud services
- Employee email patterns, roles, and public data
- Previously leaked or dark-web-available credentials
- Domain, DNS, and third-party exposure
This activity reflects how attackers identify targets – without exceeding authorized testing boundaries.
Asset Discovery & Attack Surface Mapping (Without Scope Creep)
While penetration testing remains within approved scope, reconnaissance may identify previously unknown or undocumented external assets associated with the organization. Next, we build a true picture of your external footprint, including:
When this occurs, Rebyc Security does not exploit assets outside of scope. Instead, we:
- Document the exposure
- Validate relevance and ownership
- Highlight the risk and recommended next steps
This approach mirrors real-world attacker behavior while maintaining strict authorization and control.
Targeted Scanning & Service Enumeration
Unlike broad, noisy scans, penetration testing uses:
- Precision port scanning
- Service fingerprinting
- Controlled validation to avoid disruption
The goal is realism — not volume. Testing is designed to avoid detection, just as real attackers attempt to do.
Vulnerability Validation & Exploitation
Findings are manually reviewed and safely tested to determine:
- Is the vulnerability real?
- Is it exploitable in this environment?
- What level of access does it actually provide?
Where appropriate, exploitation is performed to demonstrate impact, not just existence.
This is where vulnerability assessments stop — and real testing begins.
Attack Chaining & Impact Analysis
Modern breaches rarely rely on a single flaw.
External penetration testing evaluates how issues chain together, such as:
- Credential exposure → VPN access → internal pivot
- Misconfiguration → cloud service access → data exposure
- Weak perimeter control → identity compromise
This attacker-centric perspective is something automated tools simply cannot replicate.
Reporting That Matters to Executives and Regulators
A Rebyc external penetration test report includes:
- Clear executive-level risk summaries
- Documented attack paths with supporting evidence
- Business-aligned impact explanations
- Custom, environment-specific remediation guidance
We also conduct a live exit briefing with IT leadership and executives — ensuring findings are understood, prioritized, and actionable.
The Bottom Line
An external vulnerability assessment tells you:
“Here’s what a scanner detected within scope.”
An external penetration test tells you:
“Here’s how an attacker would realistically break in — today.”
In a threat landscape dominated by credential abuse, assumed-breach scenarios, and identity-driven attacks, the difference matters more than ever.
If your organization is relying solely on automated scanning to assess external risk, you may be testing compliance — not security.