This week, Instructure Holdings – the company behind Canvas LMS, one of the most widely deployed learning management systems in the world – officially confirmed a cybersecurity incident involving unauthorized access to user data. The breach has since been claimed by ShinyHunters, a prolific and sophisticated extortion group with a track record of high-profile attacks. The group alleges access to data belonging to approximately 275 million individuals across roughly 9,000 schools worldwide, totaling 3.65 TB of data.
Whether or not those numbers hold up to scrutiny, the core facts are significant: names, email addresses, student ID numbers, and user messages were accessed. And the deadline ShinyHunters set for their ransom demand – May 6–7, 2026 – has now passed.
This is not a drill. This is the operational reality of what happens when a vendor trusted by millions of students and educators becomes a target.
What We Know
Instructure has confirmed unauthorized access occurred and stated that the incident has been contained. They report that credentials have been revoked, patches deployed, keys rotated, and monitoring enhanced. According to their official status page, passwords, dates of birth, government IDs, and financial data were not among the compromised information.
What was accessed – names, emails, student IDs, and messages – may not sound alarming at first glance. But in the hands of a sophisticated threat actor, that data is a phishing kit. It’s the raw material for targeted social engineering, credential stuffing campaigns, and impersonation attacks against students, faculty, and administrators.
ShinyHunters doesn’t just exfiltrate data. They operationalize it. Education institutions that haven’t acted yet should treat affected users as already at elevated risk.

Why Education Is a High-Value Target
K-12 districts and higher education institutions are among the most underprotected environments in the threat landscape. Budget constraints limit security staffing and tooling. Student and faculty turnover creates constant identity management challenges. And the open, collaborative nature of academic environments – the very thing that makes them valuable – creates natural friction against restrictive security controls.
For threat actors, education institutions represent a relatively soft target with high data density. A single LMS deployment may hold data on tens of thousands of users. Credentials obtained from an education breach are routinely tested against banking, healthcare, and enterprise systems – because people reuse passwords, especially students.
The ShinyHunters claim of 275 million affected individuals is breathtaking in scope. Even if the actual number is a fraction of that, the combination of stolen identifiers and personal messages creates meaningful downstream risk for every institution on that list.
What Affected Institutions Should Do Right Now
If you support organizations using Canvas – whether you’re an IT administrator, a managed service provider, a compliance officer, or a technology consultant – here’s a practical checklist:
- Contact your Instructure account team. Get institution-specific guidance on scope and recommended actions. Don’t rely solely on public statements.
- Communicate proactively with end users. Students, faculty, and staff should be advised to monitor accounts for suspicious activity, update passwords (especially if reused elsewhere), enable multi-factor authentication wherever possible, and stay alert for phishing attempts that may reference the breach.
- Audit third-party integrations. Canvas connects to a wide ecosystem of tools. API keys and OAuth tokens may need to be rotated or reauthorized.
- Document your response. For institutions subject to FERPA or state-level data protection requirements, a documented incident response supports both compliance and defensibility.
Where Rebyc Security Fits In
At Rebyc Security, we work with organizations in highly regulated environments – financial institutions, healthcare organizations, and increasingly, education-adjacent entities – to validate that their defenses actually hold up before an adversary tests them for real.
The Canvas breach is a reminder that third-party risk doesn’t stop at vendor selection. The question isn’t just “does our vendor have good security?” – it’s “what happens to us when they don’t?”
Here’s how our services apply directly to situations like this:
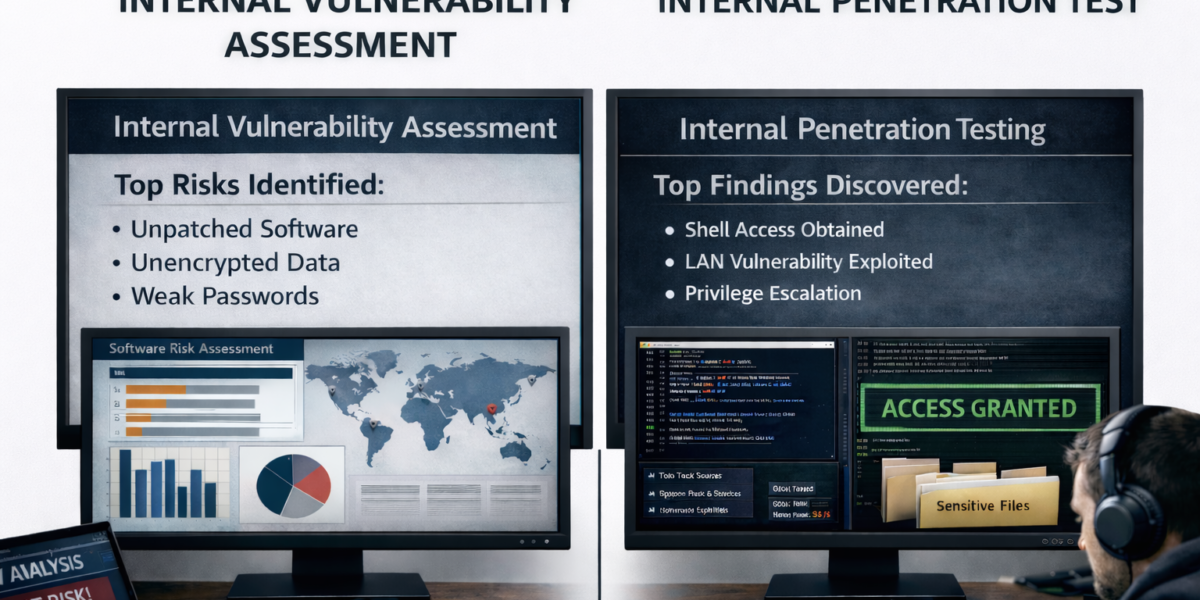
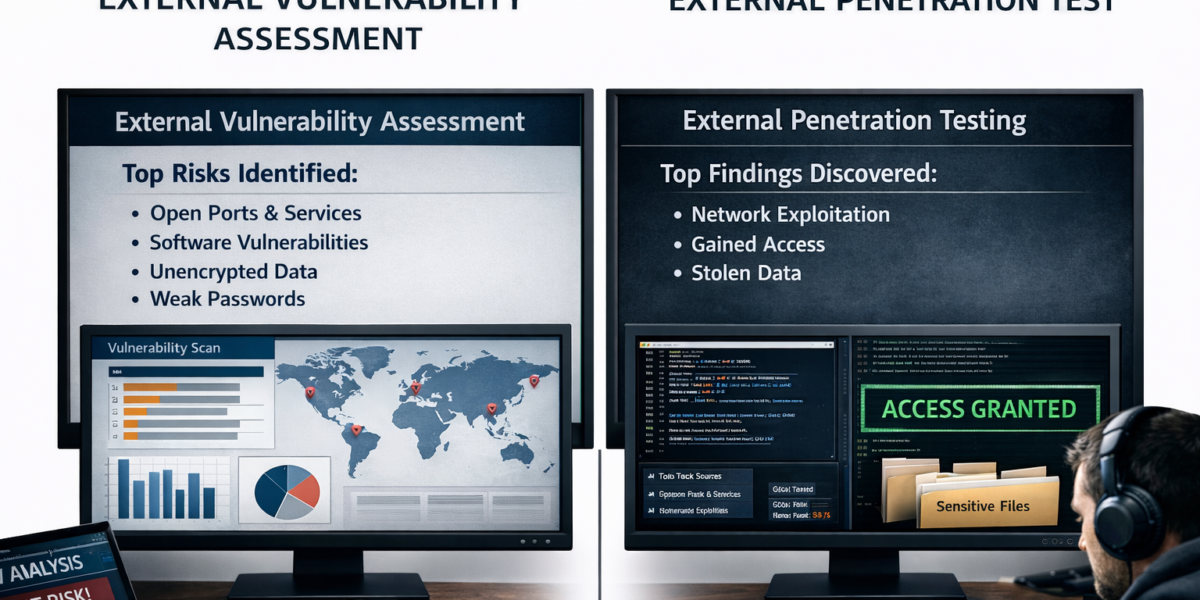
- Penetration Testing & Assumed Breach Testing: Once attackers have names, emails, and institutional identifiers, they have the foundation for credential attacks and social engineering. We simulate exactly these scenarios – testing whether your environment can detect and contain an adversary who’s already past the perimeter using realistic, attacker-grade techniques.
- Social Engineering & Vishing Assessments: Breached data fuels phishing and vishing campaigns. We test your staff’s resilience against these tactics before real attackers do – using the same types of pretexts that threat actors like ShinyHunters use to monetize stolen data.
- Web Application Security Testing: If your institution or your clients have custom integrations built on top of Canvas or similar platforms, those integrations carry inherited risk. We test whether those connections introduce exploitable vulnerabilities.
- Cloud Security Configuration Testing: Misconfigured cloud environments are a leading root cause of data breaches across all sectors. We assess whether your cloud infrastructure is hardened against the kinds of access patterns that enable breaches like this one.
The time to test your defenses is before an incident, not after. But post-breach is also a legitimate inflection point – organizations that have just watched a trusted vendor get compromised are often more ready to have a serious conversation about their own security posture.
The Bigger Picture
Vendor transparency matters. Instructure deserves credit for confirming the incident and providing actionable guidance. That’s not always the default response, and it’s worth acknowledging.
But transparency from vendors doesn’t substitute for an independent view of your own risk. Every organization that relies on third-party platforms – and that’s essentially every organization in 2026 – needs to have a clear answer to the question: if my vendor gets breached, what’s my exposure, and how would I know?
If you’re an education institution, a technology partner supporting education clients, or any organization evaluating your third-party risk posture in the wake of this incident, we’d welcome the conversation.
Stay secure.
Instructure status page: https://status.instructure.com/incidents/9wm4knj2r64z