Originally published October 14, 2016 — Updated for today’s threat landscape
This is an updated edition of one of our original posts from our first year in business. While the tools, threats, and environments organizations operate in have evolved significantly since 2016, one misconception remains stubbornly persistent:
An internal vulnerability assessment and an internal penetration test are the same thing.
They’re NOT.
Both are valuable. Both belong in a mature information security program. But they answer very different questions, produce very different outcomes, and serve different purposes—especially in today’s hybrid, cloud-connected, identity-driven environments.
Below, we break down the difference.
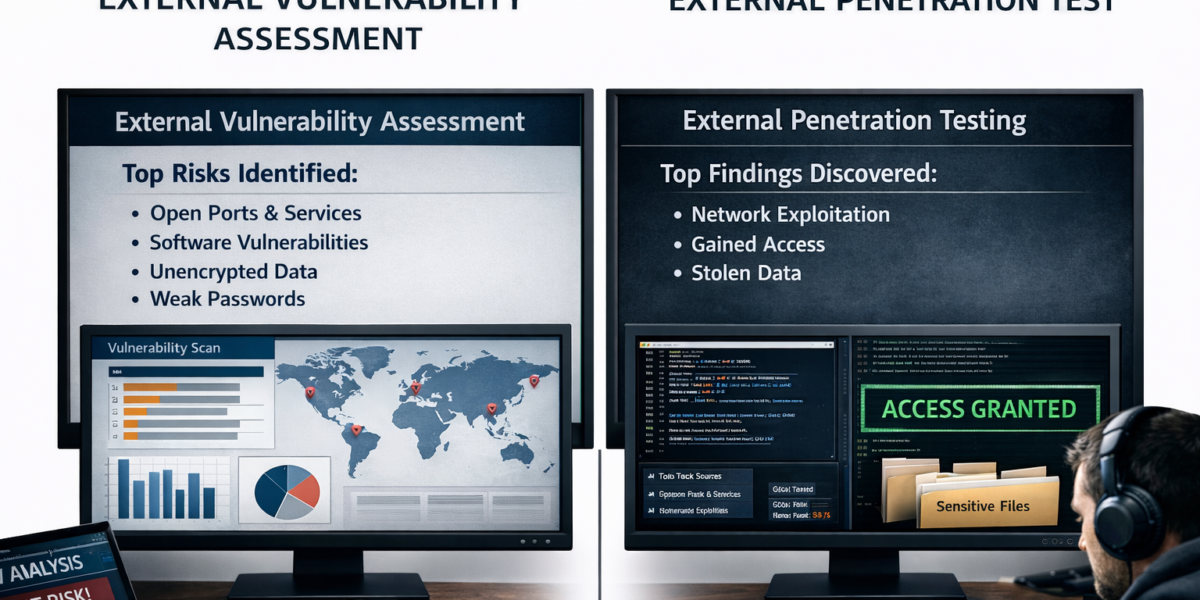
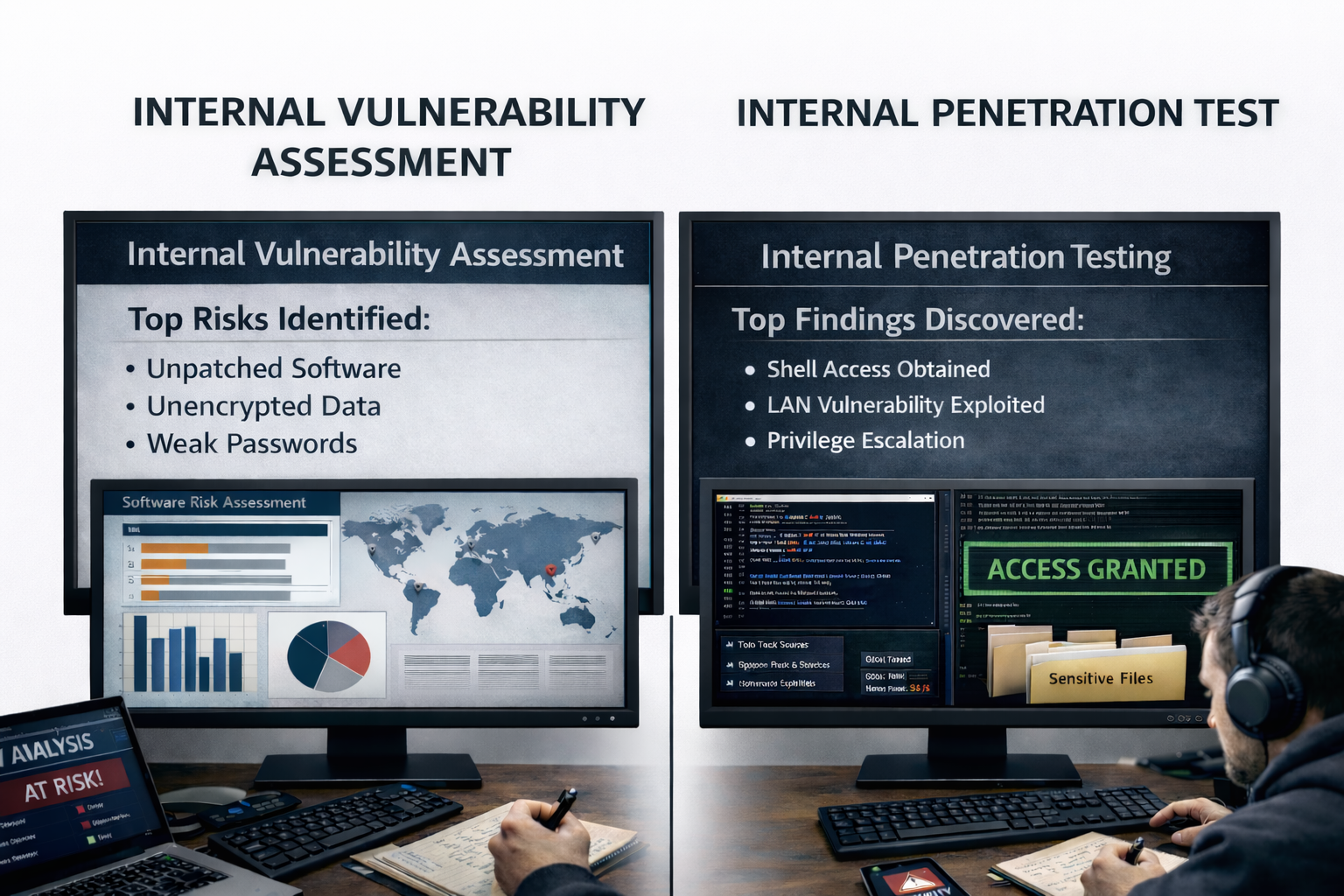
Internal Vulnerability Assessment
An internal vulnerability assessment is designed to identify known weaknesses across systems on your internal network.
Most internal vulnerability assessments rely on automated scanning tools such as Nessus, Qualys, Rapid7, or similar platforms. These tools compare systems against large databases of known vulnerabilities, missing patches, and insecure configurations. Many assessments also include authenticated scanning, allowing the scanner to log into systems and more accurately assess patch levels and configuration drift.
What an Internal Vulnerability Assessment Typically Provides
- A high-level executive summary of the most critical vulnerabilities
- Identification of missing operating system and third-party software patches
- Severity-based vulnerability listings (CVSS scoring)
- Scanner-generated reports and raw output
- General best-practice remediation guidance
The output gives leadership and IT teams a snapshot of exposure based on what is already publicly known and documented.
When Internal Vulnerability Assessments Are Most Useful
Ongoing hygiene and visibility
Performed regularly, vulnerability assessments help organizations track remediation progress over time and validate that patching and hardening efforts are working.
Third-party oversight
Many organizations outsource patching or vulnerability management. Independent assessments verify whether those services are actually being performed effectively.
Regulatory and audit requirements
Financial institutions, PCI-scoped environments, insurance providers, and other regulated organizations are often required to conduct independent vulnerability testing as part of compliance programs.
What vulnerability assessments do not tell you is whether those vulnerabilities can realistically be chained together, exploited, or used to compromise sensitive data.
That’s where penetration testing comes in.
Internal Penetration Testing
An internal penetration test starts from a very different assumption:
An attacker already has internal network access.
- Stolen credentials, compromised endpoint, malware, rogue device, VPN access, etc.
In today’s threat landscape—ransomware affiliates, infostealers, credential phishing, MFA bypasses, VPN compromise—this is no longer a hypothetical scenario. It’s a reasonable baseline.
Internal penetration testing evaluates what an attacker can actually do once inside your environment, not just what exists on paper.
Questions an Internal Penetration Test Is Designed to Answer
- Can an attacker move laterally between systems?
- Can they abuse Active Directory or identity infrastructure?
- Can segmentation controls be bypassed?
- How easily can sensitive data be accessed, staged, or exfiltrated?
- Can detection, logging, and response mechanisms identify the activity?
- How does your EDR/XDR actually respond to today’s attack techniques?
- Credential Abuse, living off the land activity, lateral movement, and privilege escalation – not just malware detection
How Internal Penetration Testing Works
Unlike vulnerability assessments, internal penetration tests are manual, adaptive, and contextual. There is no single checklist, because real attackers don’t follow one.
At a high level, testing may include:
- Gaining internal access via a controlled scenario (physical, virtual, assumed breach, or compromised credentials)
- Enumerating the environment while attempting to remain undetected
- Identifying trust relationships, misconfigurations, and weak access controls
- Exploiting vulnerabilities in sequence, not isolation
- Pivoting across systems, identities, and network segments
- Attempting privilege escalation (up to domain-level access where applicable)
- Identifying realistic paths to sensitive data or business-critical systems
In modern environments, this often includes identity abuse, cloud-connected services, endpoint security evasion, and misconfigured security tooling—not just missing patches.
What an Internal Penetration Test Delivers
- An executive summary focused on business impact
- Clear documentation of attack chains, not just findings
- Evidence of what was accessed, how, and why it mattered
- Prioritized, context-specific remediation guidance
- Insight into detection gaps—not just prevention gaps
This is where organizations learn the difference between:
“We have controls”
and
“Our controls actually work together under pressure.”
Why the Difference Matters More Today Than Ever
AIn 2016, security programs focused heavily on perimeter defenses and patching.
In 2026, most breaches:
- Abuse valid credentials
- Bypass MFA through token theft or session hijacking
- Exploit misconfigurations, not zero-days
- Move laterally using legitimate tools and access paths
A vulnerability scan may show a “clean” environment, while a penetration test reveals that an attacker can still traverse the network, escalate privileges, and access sensitive data without triggering alerts.
Final Thought
An internal vulnerability assessment tells you what exists.
An internal penetration test shows you what’s possible.
Organizations that rely on one while ignoring the other are only seeing part of the picture.
At Rebyc Security, every internal penetration test concludes with a live exit discussion with technical teams and leadership—walking through what was done, what was learned, and what actually reduces risk. We believe strong security programs are built on clarity, realism, and continuous improvement, not check-the-box testing.
If your goal is confidence—not just compliance—the distinction matters.