Do you Yahoo? Remember that slogan back in the 90’s in the Yahoo commercials? Well, you wouldn’t be alone if you do Yahoo, or did at least. Per SimilarWeb, Yahoo.com is still the most popular news and media website and the 5th most popular site overall. The Yahoo sites get over almost 6 billion visits a day, but unfortunately, those numbers are trending downward due to their security breach disclosure.
 This past December, Yahoo announced they announced that over 1 billion subscribers had potentially been impacted by the breach. This, coming after a September 2016 announcement that 500 million user accounts had been hacked in a separate breach. Making matters worse, the actual attacks, dated to 2013 and 2014. That means, those impacted, may not have known for 2 – 3 years. Just yesterday, the SEC announced it is looking into Yahoo’s customer notification timeframes for the breaches.
This past December, Yahoo announced they announced that over 1 billion subscribers had potentially been impacted by the breach. This, coming after a September 2016 announcement that 500 million user accounts had been hacked in a separate breach. Making matters worse, the actual attacks, dated to 2013 and 2014. That means, those impacted, may not have known for 2 – 3 years. Just yesterday, the SEC announced it is looking into Yahoo’s customer notification timeframes for the breaches.
What kind of impact can that have on your company? Well, if you are Yahoo and you have a $4.8B offer on the table from Verizon, it can mean Verizon wants a serious discount, if they even follow through on the deal at all. Additionally, it impacts the value of the subscriber base that Verizon thought they were getting. Do you think all those with Tumblr, Yahoo Finance and Yahoo Mail accounts are going to hang around considering the laxed security practices Yahoo apparently had in place? Doubt it.
So, what do you do to preserve your organization’s value if you’ve been breached?
Do these 3 steps immediately:
- Notify the proper IT personnel and management to let them know that account details have been leaked.
- Give as much detail about what types of information the account had access to.
- Change the affected password(s). Also, change any business or personal account passwords that are using a similar (or the same) password.
- Attackers often attempt to use compromised credentials on other well-known services.
- If it was due to a vendor, reach out to your vendor contact and gain an understanding as to what they are doing to mitigate the breach.
- Your organization’s incident response plan should have these contacts available.
There are several cases where Yahoo managed email services for Verizon.net, AT&T and others. So, what if you had a vendor, like Yahoo, who had a massive breach that may have impacted your customer base? While there is no silver bullet to prevent this, there are some steps that your organization can take to increase security when working with vendors.
Below are some tips to take when working with a vendor:
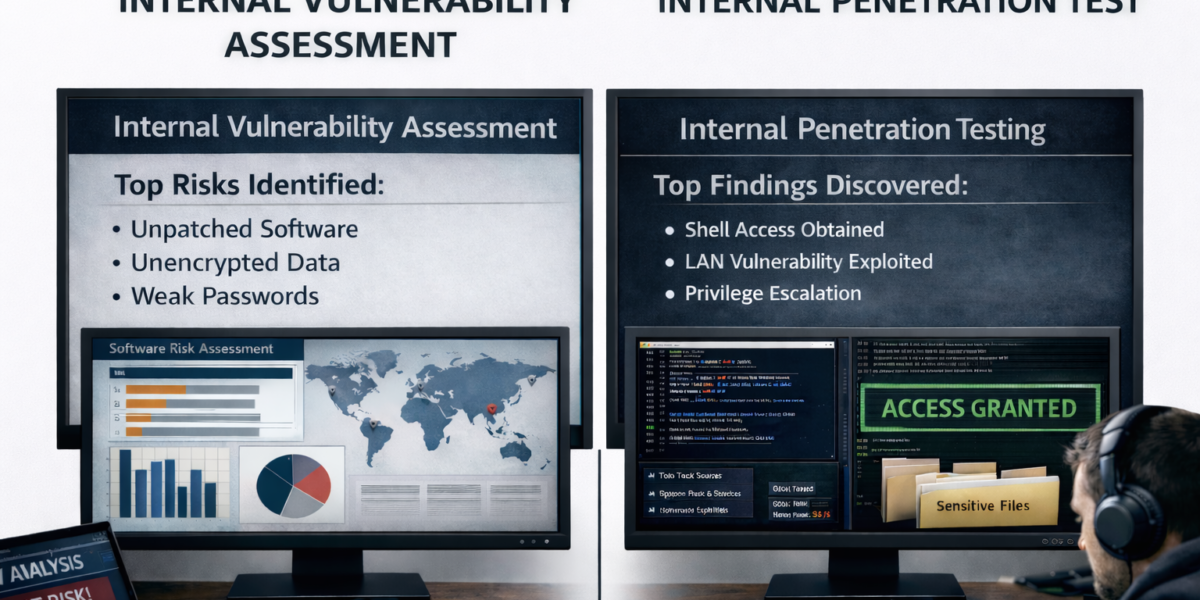
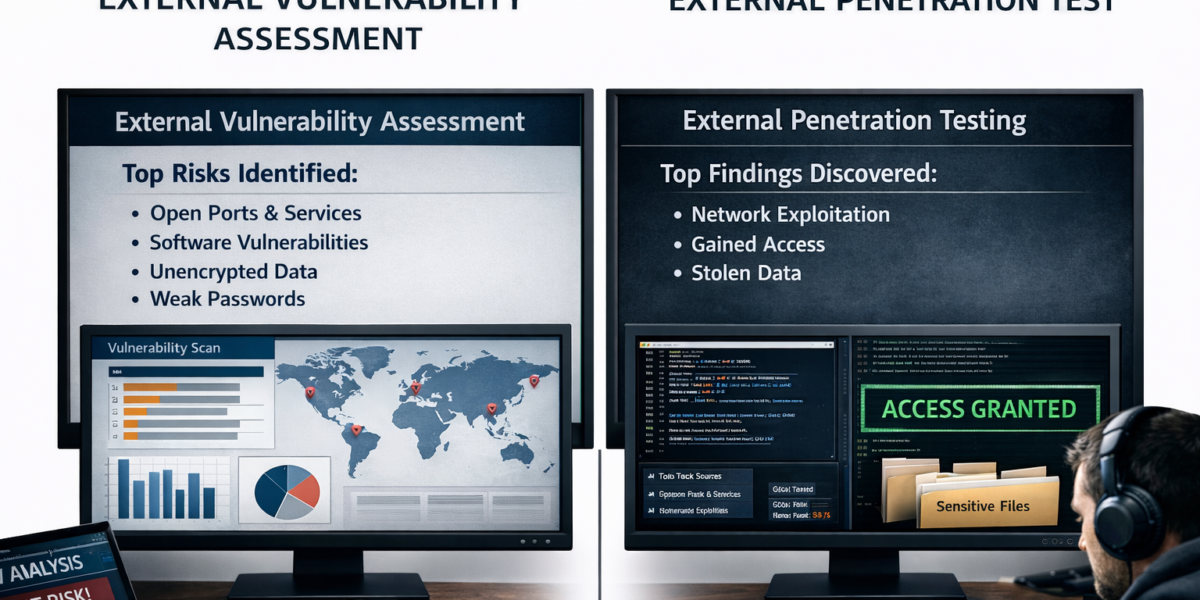
- Perform thorough due diligence, including reviewing the vendor’s SSAE-16/SOC reports and penetration test results.
- If they provide access through a portal, ask if multi-factor authentication is available.
- At a minimum, a strong lockout policy should be in place for the portal account.
- Use at least a 15-character complex password.
- Typically, passwords are dumped in the form of a hash, and using a long, complex password will decrease the attacker’s chance or cracking the hash and obtaining your password.
- If your organization allows vendor access to the corporate network, understand how the vendor gains access, what controls are in place when granting such access, and what level of access your vendor has.
- If constant access is not required, accounts should be disabled until the vendor requests access.
- Ensure your contract gives your organization the right to audit your vendor. An audit can give your organization assurances that the vendor is performing their services and operations as agreed.
If you have sensitive data at risk, it’s good practice to put a solid information security program in place. We can help. Email questions you may have to info@rebycsecurity.com.