With National Cyber Security Awareness Month (NCSAM) now upon us, we thought it would be good to dispel some cyber security service related myths. All too often, in conversations with our clients, we are finding they didn’t get what they thought they were getting when they purchased a previous service. Or worse, they don’t even realize it. Throughout October, we’ll be posting some blogs breaking down some of the more prevalent versions of these myths.
MYTH:
AN EXTERNAL PENETRATION TEST IS THE SAME AS AN EXTERNAL VULNERABILITY ASSESSMENT
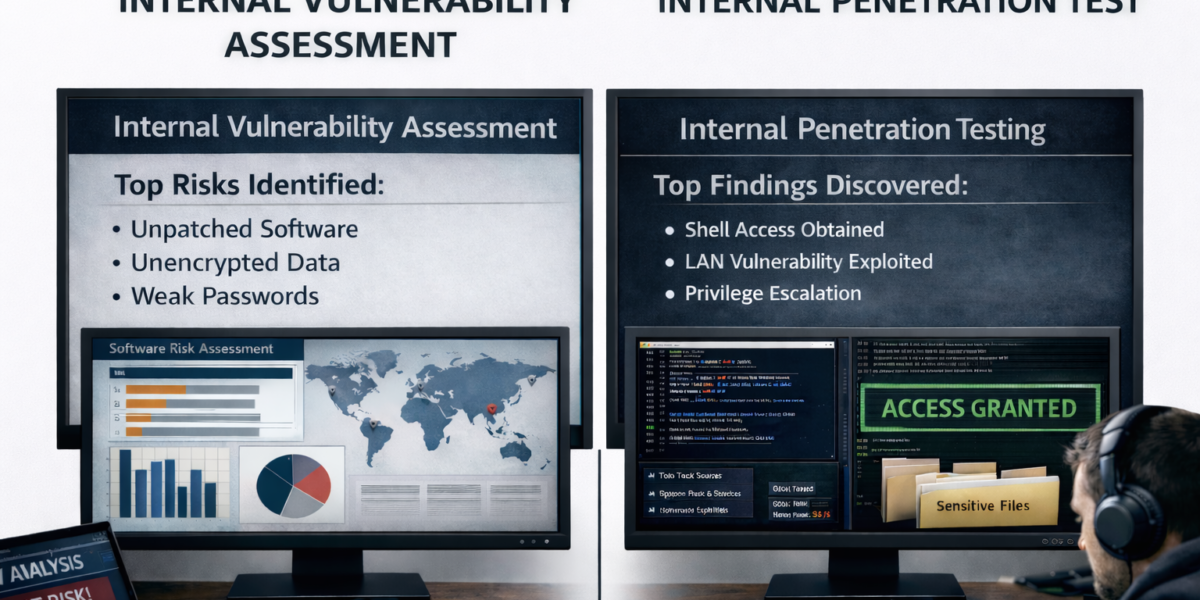
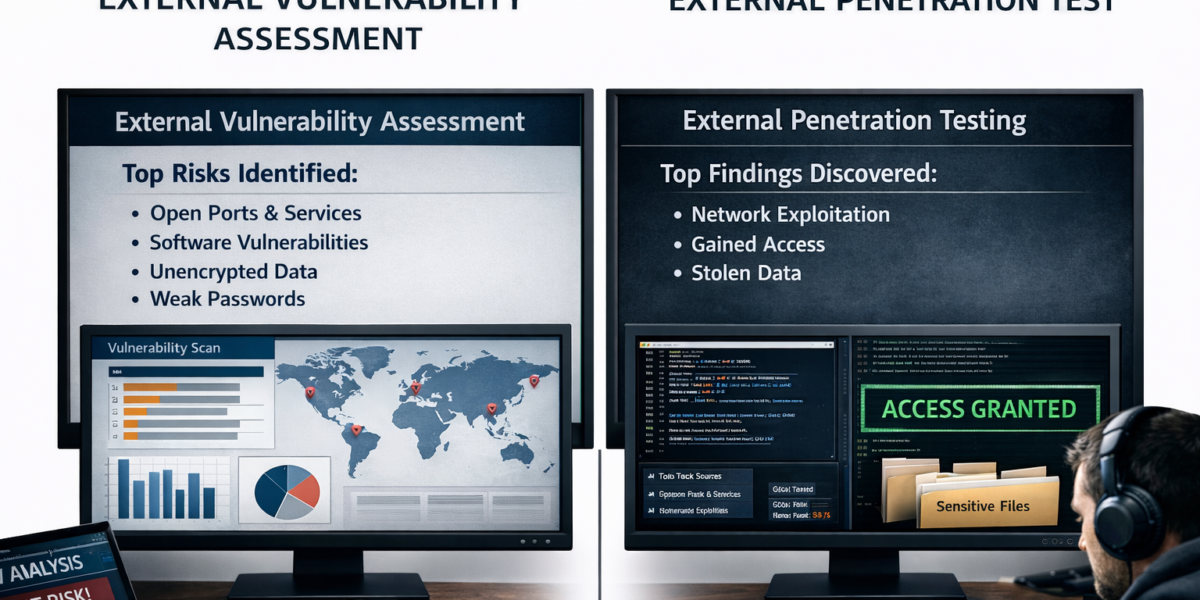
This is something we hear a lot. We’ll get a call from a prospect requesting information on an “external vulnerability assessment,” but when we start to go through their actual needs, we find they are seeking an external penetration test. The two are separate and distinct and while they may be combined to provide a robust service, they have some key differences. In the breakouts below, we’ve outlined some key components of each:
External Vulnerability Assessment
An External Vulnerability Assessment typically utilizes a third-party scanning tool such as Nessus, Qualys, or other similar third-party vulnerability scanners. These applications allow for a quick, automated scan of your organization’s external footprint for known vulnerabilities. Generally, the final report(s) turned over to the client will include:
- High-level executive summary of the most critical vulnerabilities
- General best practices recommendations for vulnerability remediation
- Raw output from the vulnerability scanning application
In some cases, that may be all your organization is looking for at the time, which makes the assessment an efficient way to obtain those results. However, a few questions that should be asked are:
- What about unknown vulnerabilities and/or misconfigurations?
- Do we have hosts/accounts that have been compromised already?
- Did we whitelist the scanning service or allow our IDS/IPS to block the traffic?
- Did we obtain results for all IP addresses that were in-scope?
- How accurate were the results that were presented to us?
If you are uncomfortable with answering some of the above questions or prefer a more in-depth picture of your organization’s external footprint, we recommend an External Penetration Test which is outlined below.
- Reconnaissance Phase
- The penetration tester will perform various manual and automated scans of the Internet, news groups, social media, etc. to locate your organization’s externally facing resources and employee information. All relevant information will be tested against previously known leaks made publicly available.
- Discovery Phase
- During this phase, the penetration tester will perform passive IP reconnaissance, DNS Interrogation, and IP block lookups to gain a full picture of externally available assets. Relevant targets will be checked passively against non-commercial scanning tools and informative websites. Any vulnerabilities that are discovered may be exploited at this time.
- Scanning Phase
- The penetration tester will utilize previously gathered information to create specific, targeted port-scans to help avoid detection. If your organization prefers, the pen tester can be whitelisted after their targeted scans to allow for an even better picture of your organization’s external environment. All active ports will be enumerated and underlying services will attempt to be identified.
- Vulnerability Analysis Phase
- All identified vulnerabilities will be manually reviewed to ensure that there is no risk of creating a denial-of-service or other service disruptions to the affected resource. If no vulnerabilities have been discovered, the penetration tester may utilize an automated vulnerability scanner such as Nessus, Qualys, or similar software.
- Exploitation
- The penetration tester will attempt to exploit the discovered vulnerabilities at this time. All attempted exploits will be manually verified to determine if the vulnerability was successfully exploited.
After the testing has concluded, a detailed report will be written that should include the following:
- An executive summary for the most damaging vulnerabilities that were discovered and possibly exploited.
- A detailed description of attack chains and all supporting evidence will be included within the report.
- Custom mitigation techniques that are tailored for your organization.
At Rebyc Security, we always include an exit call with your organization’s IT personnel and key executives to talk through the report in detail and answer any questions you may have. Additionally, Rebyc Security wants to create a sound relationship with our clients, which is why we make ourselves available to you year-round, to answer any questions that may arise throughout the year.
Have questions? Let’s talk – schedule a free consultation with us today: