This is our second National Cyber Security Awareness Month (NCSAM) post where we seek to dispel some myths about cyber security services. Throughout October, we’ll be posting some blogs breaking down some of the of the more prevalent versions of these myths we are seeing in the market.
MYTH:
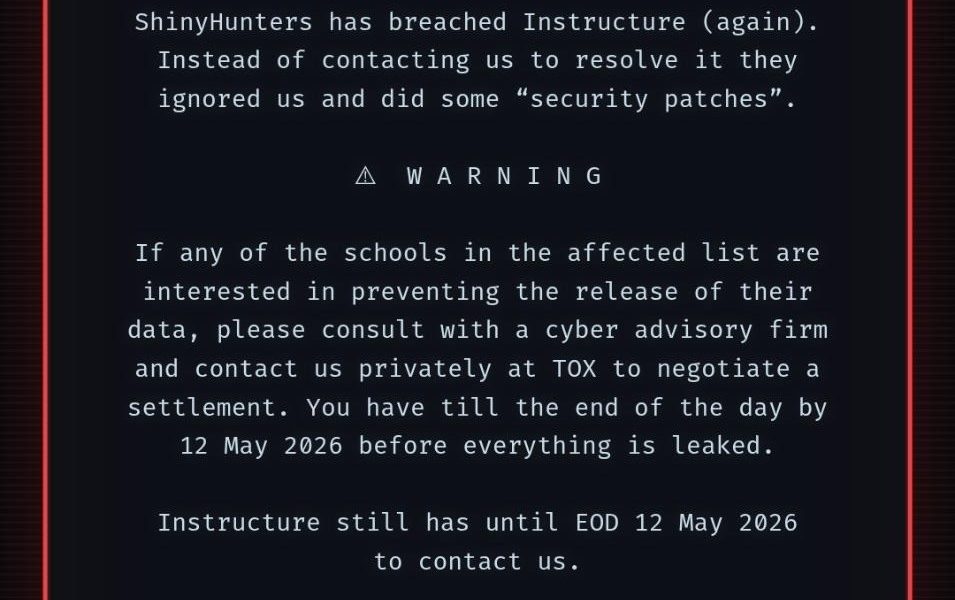
AN INTERNAL VULNERABILITY ASSESSMENT IS THE SAME AS AN INTERNAL PENETRATION TEST
While both tests are tremendously valuable and should be included into any organization’s Information Security Program, the reasons for conducting these tests and the information obtained from these reports will vastly differ. In the breakouts below, we’ve outlined some key components of each:
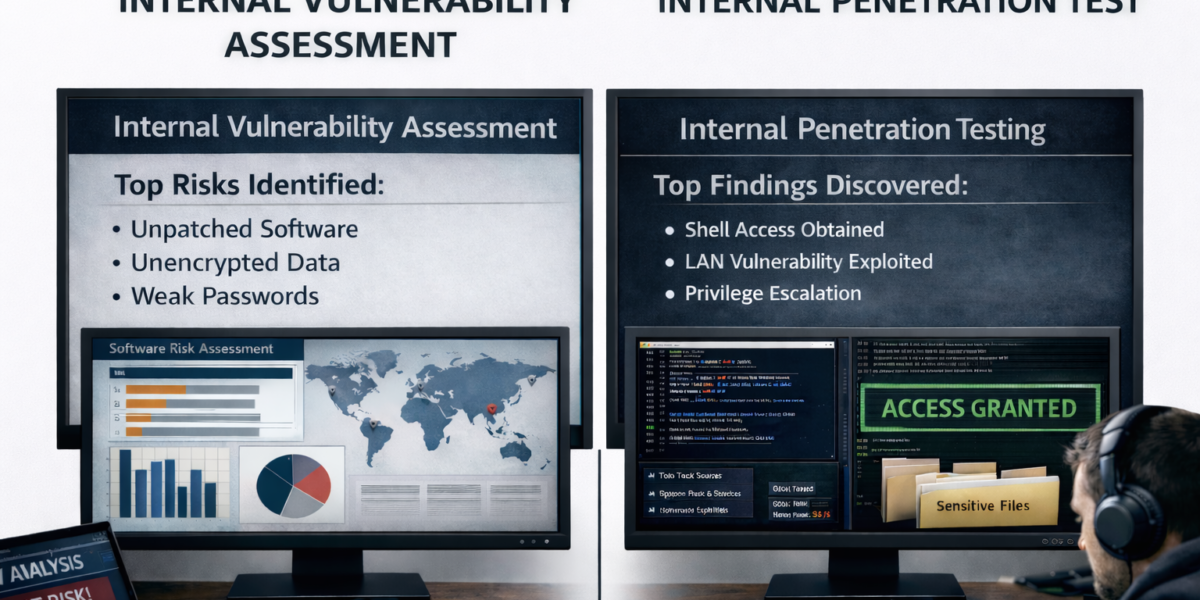
Internal Vulnerability Assessment
An Internal Vulnerability Assessment typically utilizes a third-party scanning tool such as Nessus, Qualys, or other similar third-party vulnerability scanners. These applications allow for a quick, automated scan of your organization’s internal network for known vulnerabilities. Additionally, many Internal Vulnerability Assessments will include an authenticated patch management scan, to determine your organization’s overall patch levels. Missing operating system or third-party software patches are typically a large contributor to vulnerabilities existing on a network. Generally, the final report(s) turned over to the client will include:
- High-level executive summary of the most critical vulnerabilities and missing patches
- General best practices recommendations for vulnerability remediation
- Application generated reports from the patch management software
- Raw output from the patch management software
- Raw output from the vulnerability scanning application
The results obtained from the Internal Vulnerability Assessment should give management solid insight into the risk levels associated with the vulnerabilities and missing patches on their internal network. In addition to providing an excellent snapshot, this test can also be used to satisfy goals such as the ones listed below:
- Monitor Remediation Efforts
- When performed regularly, Internal Vulnerability Assessments can help you determine if your organization’s remediation efforts are being performed in a timely and efficient manner. Results from this test can also be used to generate remediation plans.
- Monitor your Third-Party
- Many organizations now outsource their vulnerability and patch management functions to an outside third-party. However, how many actually verify they are getting what they are paying for?
- Independence
- Financial institutions, PCI-Compliant retailers, insurance agencies… and the list goes on. Many more organizations are now being required to conduct independent, third-party testing to satisfy regulatory requirements.
Concerned with how vulnerable your organization is to an attacker gaining access to your internal network or a rogue employee with physical and logical access to your network? Then continue reading below to find out more details around an Internal Penetration Test:
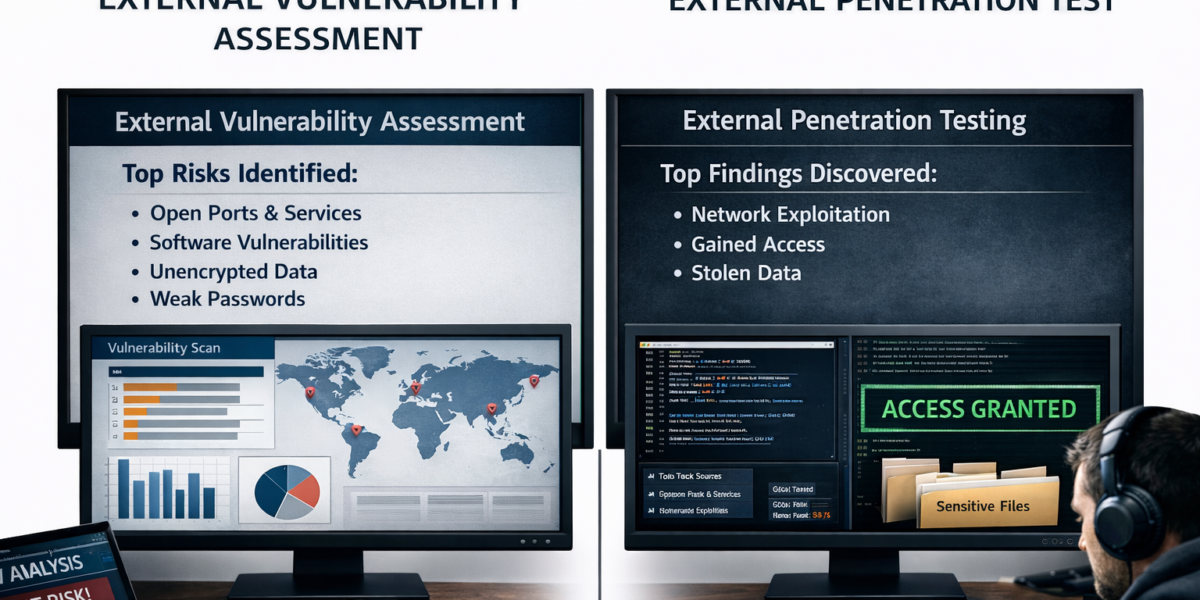
An Internal Penetration Test makes the assumption that an attacker has gained logical access to your organization’s network. Given the amount of breaches in 2016 alone, we can conclude that this is a current security issue. Internal Penetration Tests should be customized to your organization’s specific requirements and desired outcome of the testing.
An Internal Penetration Test is an excellent step to take when considering these questions:
- Are you looking to test your network segmentation?
- Do you want to test assuming a full domain compromise?
- Or, are you checking to see how secure your sensitive information is?
Since many Internal Penetration Tests are customized, there’s no real set of standard steps that are followed for every engagement. Below are some of the steps a consultant might take to provide a sound test:
- At a high-level, a consultant posing as an “attacker” will gain access to an organization’s internal network.
- This can be done through physical device, virtual machine, malware, etc.
- Once on the network, the consultant will try to gain as much useful information about the internal network as possible while remaining unnoticed.
- Next, the consultant will use the information gathered to formulate attacks and to further his foothold on the internal network.
- If successful, the consultant will be able to pivot and access additional network resources and begin to look at options to move the sensitive data off network.
- If requested, the consultant may also attempt to “sniff” network traffic to obtain passwords in clear-text or password hashes and attempt to elevate to domain administrator status as well.
After the testing has concluded, a detailed report will be written that should include the following:
- An executive summary for the most damaging attacks that were performed and resulted in compromise of sensitive information.
- A detailed description of attack chains and all supporting evidence.
- Custom mitigation techniques that are tailored for your organization.
At Rebyc Security, we always include an exit call with your organization’s IT personnel and key executives to talk through the report in detail and answer any questions you may have. Additionally, Rebyc Security wants to create a sound relationship with our clients, which is why we make ourselves available to you year-round, to answer any questions that may arise throughout the year.