Let’s get real for a minute – like Chris Roberts real. If you don’t know or know of Chris and you work in cybersecurity or information security, he is a good follow. His posts are always on point, relevant, and slightly scary, even to those of us who deal with this stuff daily. But they are also honest.
His latest, posted March 18, 2020, is like a throat punch – it takes your breath away for a minute. But then you realize how much it makes you THINK. His message may not be for everyone, but if you give it a read and truly think about the threats your organization is facing in these difficult times, it could be quite helpful.
And, stay tuned after for some helpful links and some steps your organization can take to help protect your staff, your infrastructure and your business.

LinkedIn: Chris Roberts
Cold Hearted Bastard…
NOW is the time to attack you
NOW is the time to take advantage of you
NOW, while you are in chaos
NOW, while you won’t notice
NOW, while you practice your BCP for real
NOW, when your WFH is flooding the helpdesk
I’d launch an email campaign or three
I’d take advantage of that empty building
I’d wardrive YOUR employees
I’d hide among the chaos
I’d attack comms
I’d attack transport
I’d hold the hospital for ransom
I’d be a warning from CDC
I’d be an update from your hospital
I’d be your insurance policy PDF
I’d be your concerned parents
I’d be your CEO playing nice…
I’d be HR with updates
I’d be your supplier
I’d be your savior…NOT.
I’m NOT nice, I’m NOT here to be nice, I’m here to help YOU get through this, to make sure that you, the organization, AND your data survives intact and doesn’t end up in my database… PLEASE think, then think again, question everything. Verify and then POSSIBLY trust only IF you’ve passed the “sidragon” filter…
Remember, I WILL strike you AT your weakest point DURING your weakest moment, and for many, that is right NOW.
‘all for now
Chris
Again, there is real and then there is Chris Roberts real. The things he brings up, they aren’t rocket science, this is exactly how the criminal hackers are going to attack your businesses, knowing full well, that you might not be at your best right now.
The headlines are already getting filled with reports of fake coronavirus websites, fake coronavirus maps, vishing campaigns asking for donations, text messages giving away iPhones, government stimulus check scams…. And so on. Below are some of the latest posts:
Coronavirus Scams: Watch Out for These Efforts to Exploit the Pandemic
Elite Hackers Are Using Coronavirus Emails to Set Traps
Live Coronavirus Map Used to Spread Malware
For some of you, this is creating significant disruption to your business, infrastructure and overall ability to service your customer base. While the list below isn’t an exhaustive list of steps you can do to protect yourselves and your business, hopefully it helps make sure you are addressing some of the challenges facing your organization today.
So, what can you do to help your company weather this storm and keep your infrastructure and staff safe? Here are a few ideas:
- Use Chris’s list as a blueprint. These aren’t just possible scenarios, they are likely. Run down his list and consider each within your organization.
- Communicate. As a matter of fact…..OVER Communicate. Send out daily emails with info on the latest attacks, what’s working, what’s not and steps for your staff to combat the attacks.
- Remind staff of the polices and procedures you have in place for remote working.
- Latest NIST Information Technology Laboratory Bulletin:
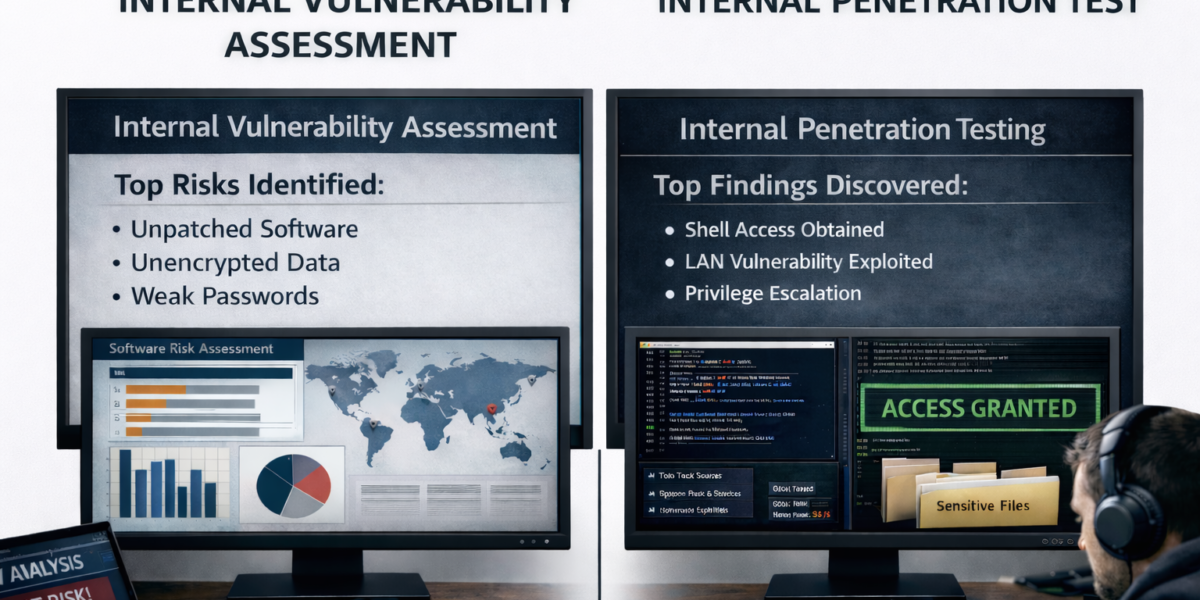
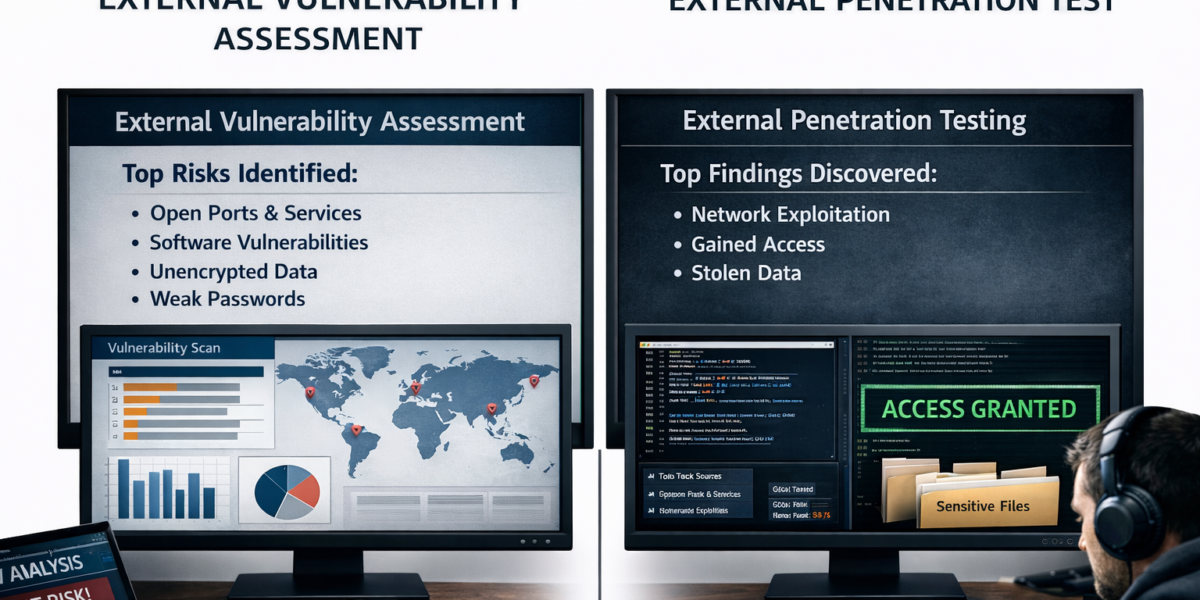
- Do you have solutions in place to address these attacks?
- VPN, Secure Wi-Fi, Data Access, Data Downloads, Flash Drives, online data storage, use of approved devices – whatever needs to be addressed……address it.
- Educate your team about corporate communication – “we would never ask you to enter your credentials into a site via email…..etc.”
- Reassure employees that you have practiced, prepared and trained for this (Assuming you have of course). It’s unprecedented, sure, but we can get through it together.
- Remind staff of the polices and procedures you have in place for remote working.
- Infrastructure. Will it continue to support the needs of your remote working staff?
- Is your bandwidth enough? Do you have a plan or an option with your provider to increase if needed?
- Do you have appropriate licensing to cover an increase in VPN? Is it secure enough?
- Are your employee’s networks secure? Strong Passwords in use? (See #2 above and educate!)
- Do you have access to your remote staff’s machines? Troubleshooting? What happens if their machines crash – do you have a plan in place to replace?
- Will your endpoint protection be enough?
- Do you have multi-factor authentication enabled where possible?
Hopefully this post has made you THINK. But don’t stop there, you need to take action and take a proactive approach. Right now, the criminals are just casting a wide net and seeing how many fish (or phish) they can catch in their net. Those fish, and their companies will quickly become targets.
Our team at Rebyc Security is here to help. Each member of our staff of consultants has 10 plus years of experience working in the information security fields, many with backgrounds both working within and consulting for highly regulated organizations. If we can help answer your questions or be a resource during these unprecedented times, please reach out.
Info@rebycsecurity.com or 704-926-6568