NEWS RELEASE
DATELINE: Charlotte, North Carolina
FOR IMMEDIATE RELEASE: June 15, 2020 — Rebyc Security today introduces cyber security penetration testing services to help proactively address new and growing insecurities in remote working arenas.
The services – designed to identify network gaps and weaknesses before cyber attackers do – will help companies reduce revenue and data losses, business disruptions, and damages to employee and brand reputations.
Rebyc Security offers these services to chief information security officers and information security officers employed by banks and credit unions as well as healthcare and insurance companies.
“The pandemic has created many new ways for cyber attackers to steal revenues and sensitive corporate and employee data by attacking the highly vulnerable networks and technologies used by remote workers,” said Patrick Barry, Rebyc Security’s chief information officer. “These new services help address a broad range of unprecedented and unusual circumstances caused by the pandemic in a proactive, methodical way.”
More virtual private network (VPN) equipment vulnerable to attacks
These profound work changes have created several rushed and disorganized remote working network arrangements and a whole new set of potential insecurities that cyber attackers can exploit.
For example, remote workers are using more virtual private network (VPN) equipment and services to connect to their corporate networks. As a result, cyber attackers have more ways to succeed in penetrating and disrupting corporate networks. One of these new services will test for security weaknesses in the VPN equipment installed within corporate offices and attempt to penetrate them.
To better understand VPN usage trends, Rebyc Security recently conducted a survey of industry professionals. Eighty-five percent of respondents said they have implemented multi-factor authentication for VPN accounts. And 78 percent said VPN appliance is part of their normal security and penetration testing efforts.
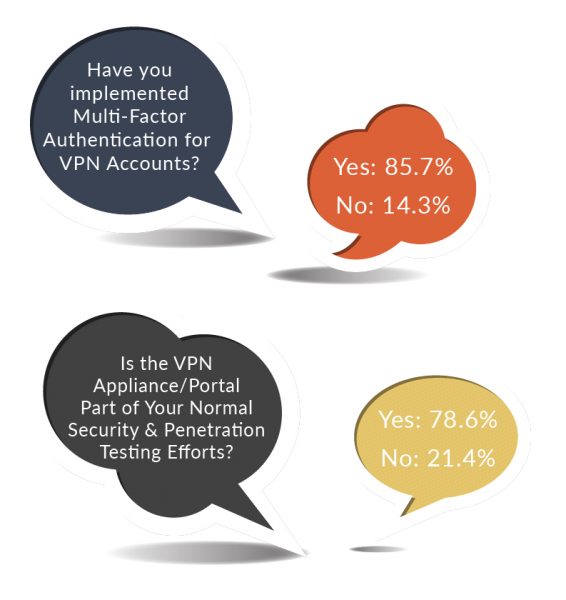
“Companies deploying all this new and highly vulnerable VPN equipment need to make sure it is as secure as possible at preventing cyber attacks,” added Barry. “Addressing this VPN security problem in the remote working environment ranks among the most important for companies to address right now.”
Cyber criminals know peoples’ guards are down
Because of the pandemic, many companies had to move their desktop and laptop PCs in the office to employees’ homes swiftly to keep businesses operating. Some bought large quantities of PCs without the normal security procedures in place for each piece of equipment.
And remote workers are more distracted than usual because their working lives have been in upheaval because of concerns about the coronavirus. They are more susceptible to clicking on malicious links and less vigilant about securing their networks.
“Cybercriminals are taking advantage of the work-from-home disruption caused by the pandemic,” he added. “They know peoples’ guards are down and are exploiting their fears and anxieties about the coronavirus and the economy.”
This difficult situation could have huge financial consequences for businesses. Companies victimized by cyber attacks of remote workers could lose millions of dollars in revenues alone. Or they can invest less than $10,000 in cyber security penetration testing services and minimize these attacks.
Read More about Rebyc Security’s Phishing and Social Engineering
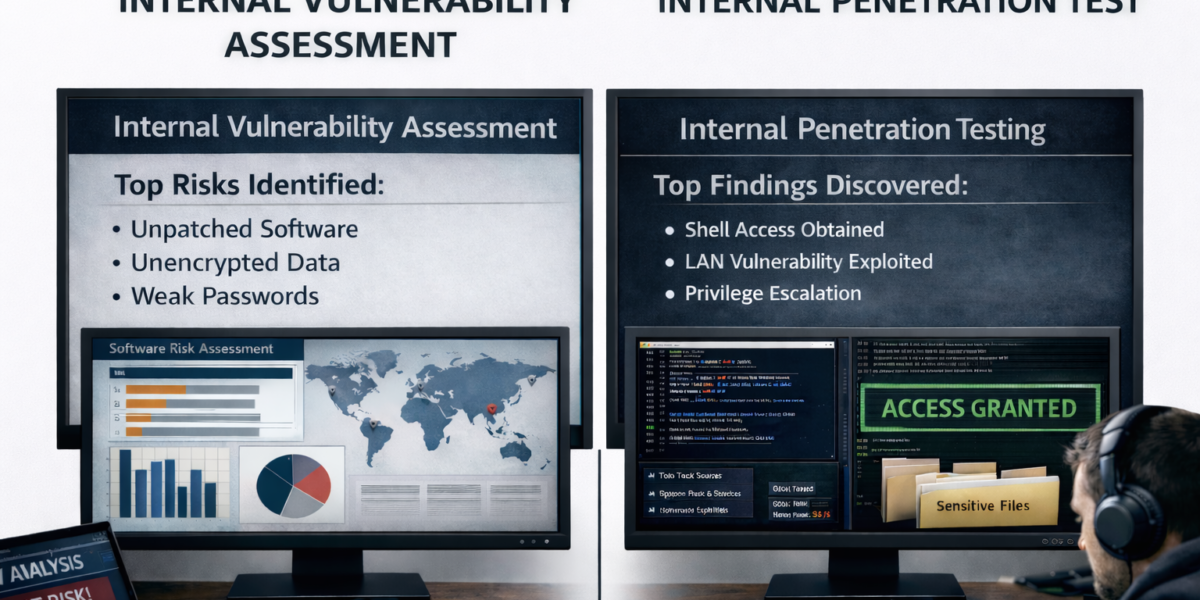
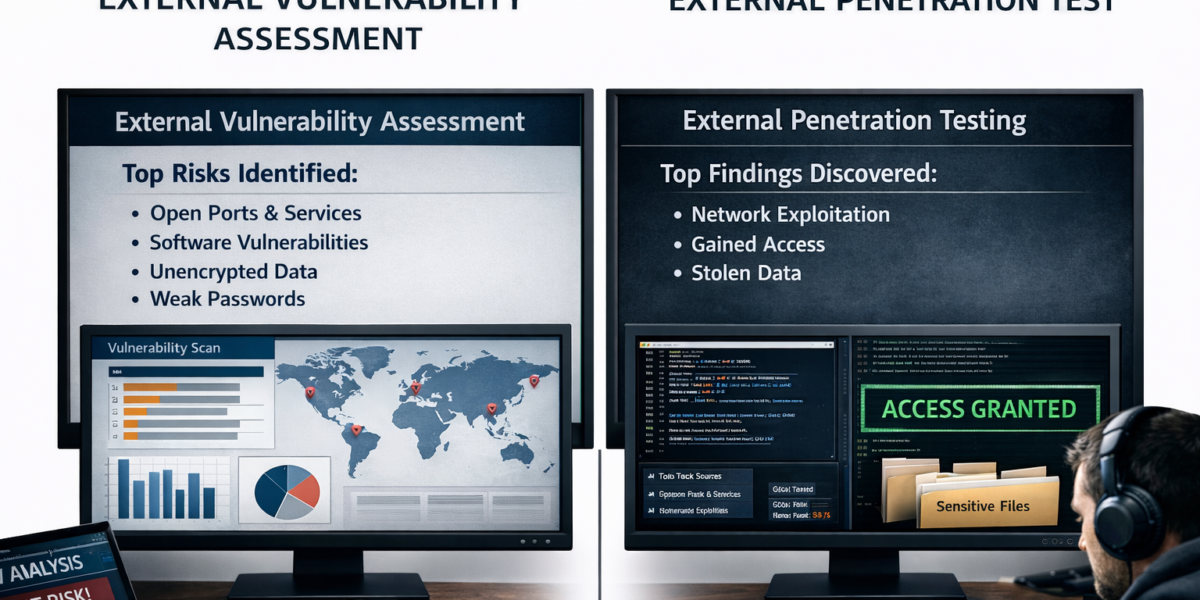
Details of penetration testing plan
The Rebyc Security remote access penetration testing plan consist of four elements: a remote access policy and procedures review; an initial phishing campaign; an external penetration test and vulnerability scan of remote access portals and appliances; and a final phishing campaign.
Remote access policy and procedures review
During this part of the plan, Rebyc consultants will review employee documentation related to remote access and the acceptable use requirements related to remote access.
The consultants will work with the appropriate IT personnel to obtain the remote access request and approval process, any security measures currently in place and password policies around remote access. Any potential deficiencies within the policies and procedures will be identified and mitigation strategies will be proposed.
Initial phishing campaign
In the initial phishing campaign, Rebyc Security consultants will work with the appropriate IT personnel to understand the company’s current remote access infrastructure and logon procedures
Based on this information, the company will execute phishing attacks, for example, on the email systems of remote working employees. These attacks are designed to entice them to click on fraudulent email links to gather sensitive information about the employees such as their PC Internet Protocol addresses, remote access and VPN credentials, and password log-in information.
External penetration test
For this test, the consultants will execute a full port scan and service listing on all remote access portals, VPN appliances, and external facing remote access resources. The company will also execute password spraying attacks against external remote access portals or VPN equipment accessible via the Internet.
Final phishing campaign
The consultants will create a phishing campaign based on the company’s previous results and knowledge of the organization. The campaign will attempt to entice employees, for example, to install a piece of malicious software. This software will allow the consultants access to the employee’s workstation or laptop with the same rights as the user.
By implementing all these tests, the consultants will test the effectiveness of spam filtering rules, Web filtering rules, endpoint protection, user access rights/permissions, policy/procedure effectiveness, and user awareness training effectiveness.
About Rebyc Security
Rebyc Security provides cyber security penetration testing services to chief information security officers and information security officers in the banking, credit union, healthcare, and insurance industries. The services help companies identify gaps and weaknesses in corporate networks before attackers do and offers recommendations for how to address them. By identifying and addressing cyber attack gaps in advance, companies reduce revenue and data losses, business disruptions, and damages to corporate and employee reputations. www.rebycsecurity.com.
Contact:
Charles Hartley
Carolina Content & Media Relations Corporation
973-590-9920