Originally published October 14, 2016 — Updated for today’s threat landscape This is an updated edition of one of our original posts from our first year in business. While the tools, threats, and environments orga...
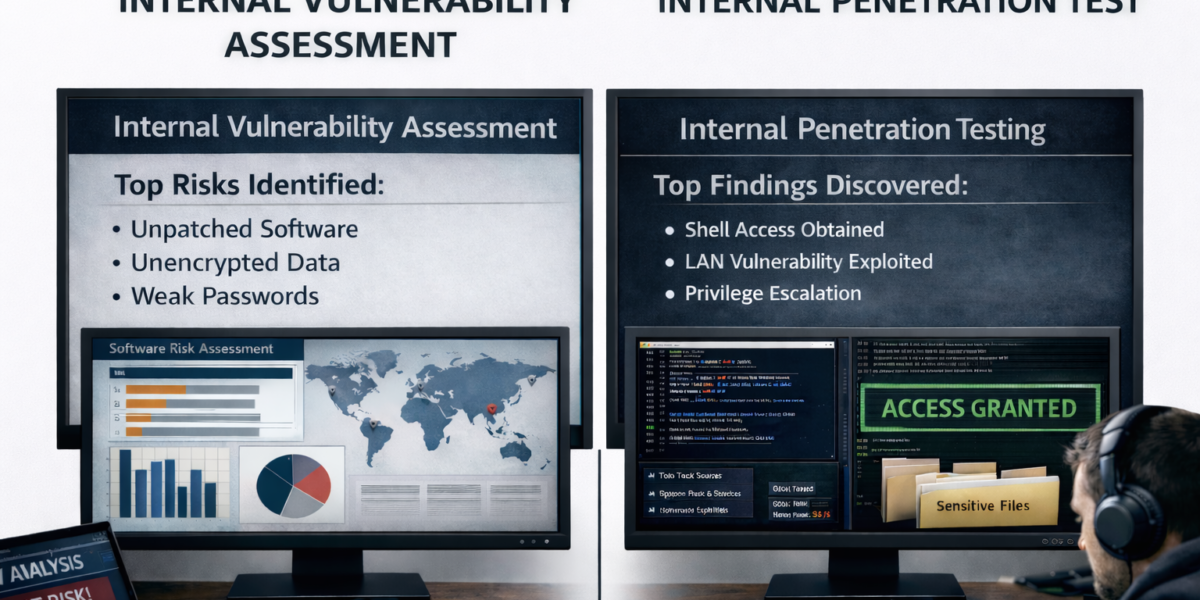
Originally Published October 6, 2016. Updated For Today’s Threat Landscape! We first wrote this blog post back in 2016 – The old line, the more things change, the more they stay the same still works –...
You’ve invested heavily in ransomware defenses. Firewalls, endpoint protection, backups, email security, and an incident response plan are all in place. On paper, your organization looks well protected. And yet, attac...
Despite widespread adoption of zero-trust architectures, advanced endpoint detection, and phishing-resistant MFA, phishing continues to be the most reliable initial access vector for attackers. Industry breach analysis c...
Team Rebyc Security spent the week of September 7-12, 2025 in sunny San Diego, CA at the Jack Henry JAC Connect Customer Conference and Cybersecurity Forum. It was an amazing week for our Rebyc Security team to get to re...
Team Rebyc Security spent the week of October 7-11, 2024 in Phoenix, Arizona at the Jack Henry Connect (#JHConnect2024) Customer Conference. It was an amazing week for our team to get to re-Connect with Clients, Partner...
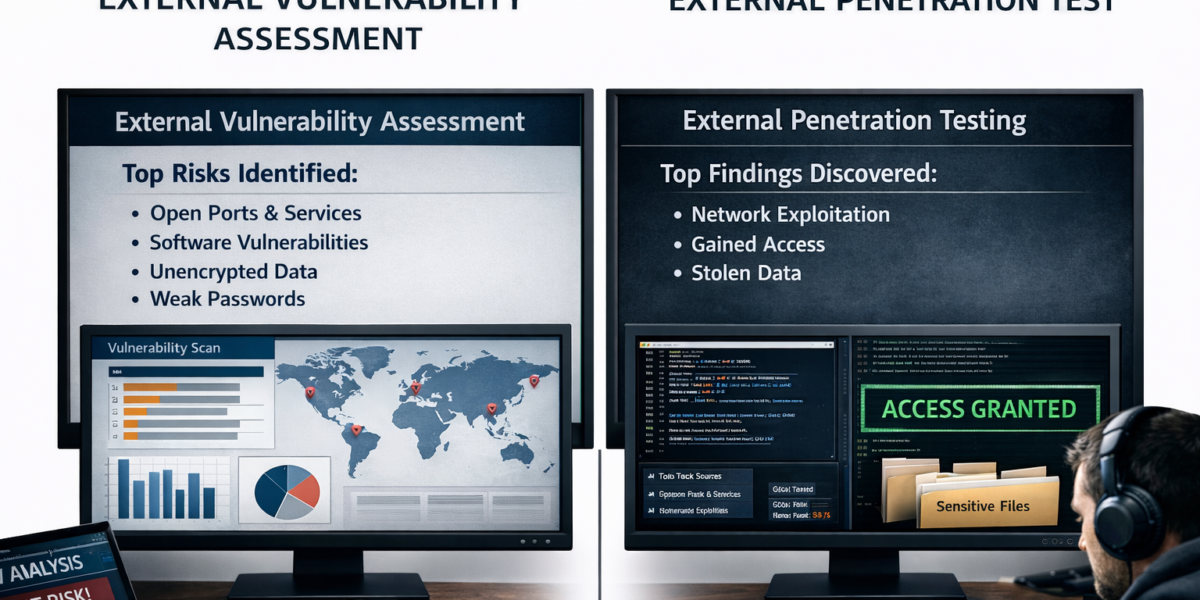
External penetration tests are a critical component of an organization’s cybersecurity strategy. They simulate real-world attacks by external hackers to identify vulnerabilities that could be exploited from outside the o...
In today’s digital landscape, security threats are omnipresent. Systems are no longer the sole targets; attackers are increasingly focusing on employees. Modern technical controls, when correctly configured, are hi...
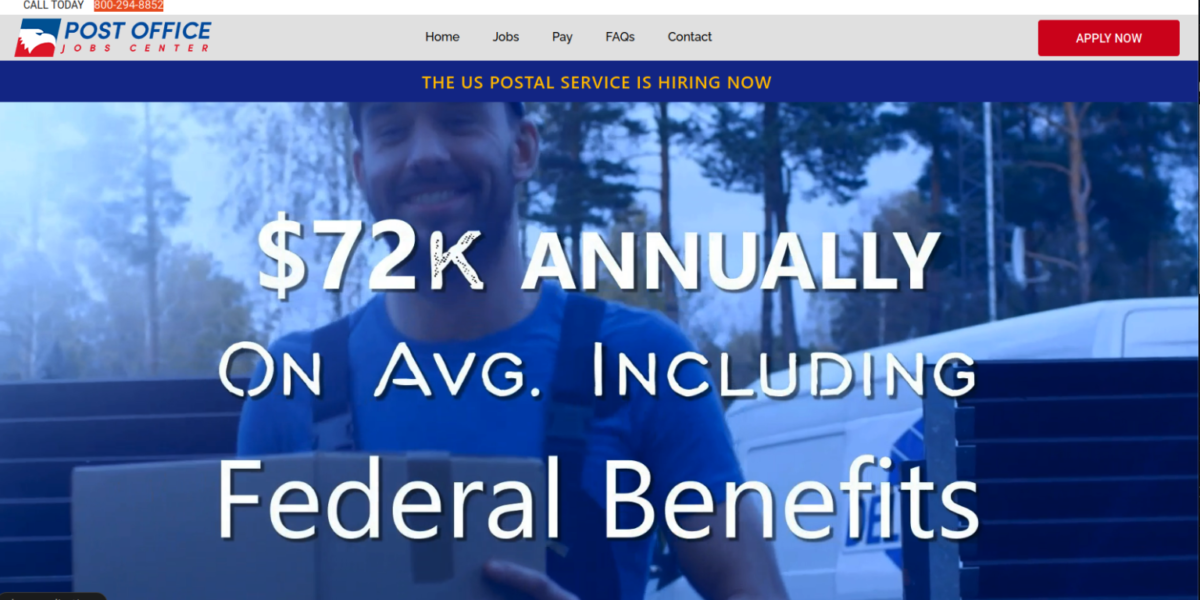
Promising Jobs at the US Postal Service US Job Services Leaks Customer Data https://krebsonsecurity.com/2023/05/promising-jobs-at-the-u-s-postal-service-us-job-services-leaks-customer-data/ Patrick Barry, Rebyc Sec...
How it’s Happening and Five Steps to Take to Protect Your Network When most people think of cutting edge cryptomining, they don’t think of using PLCs (Programmable Logic Controllers). Apparently criminal hackers and c...