Originally published October 14, 2016 — Updated for today’s threat landscape This is an updated edition of one of our original posts from our first year in business. While the tools, threats, and environments orga...
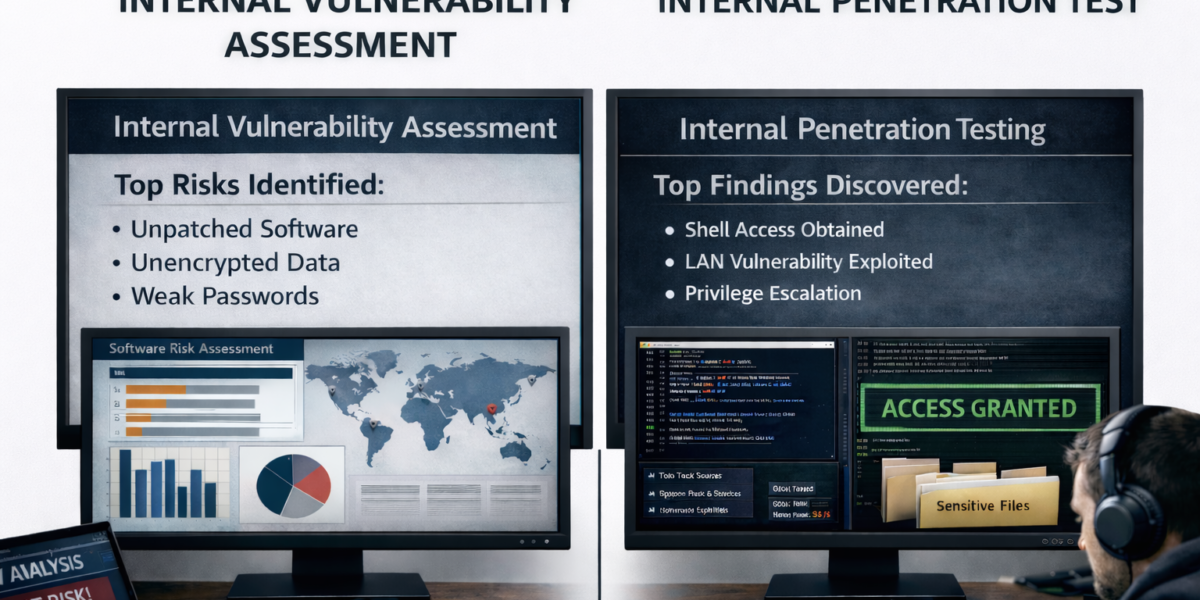
Originally Published October 6, 2016. Updated For Today’s Threat Landscape! We first wrote this blog post back in 2016 – The old line, the more things change, the more they stay the same still works –...
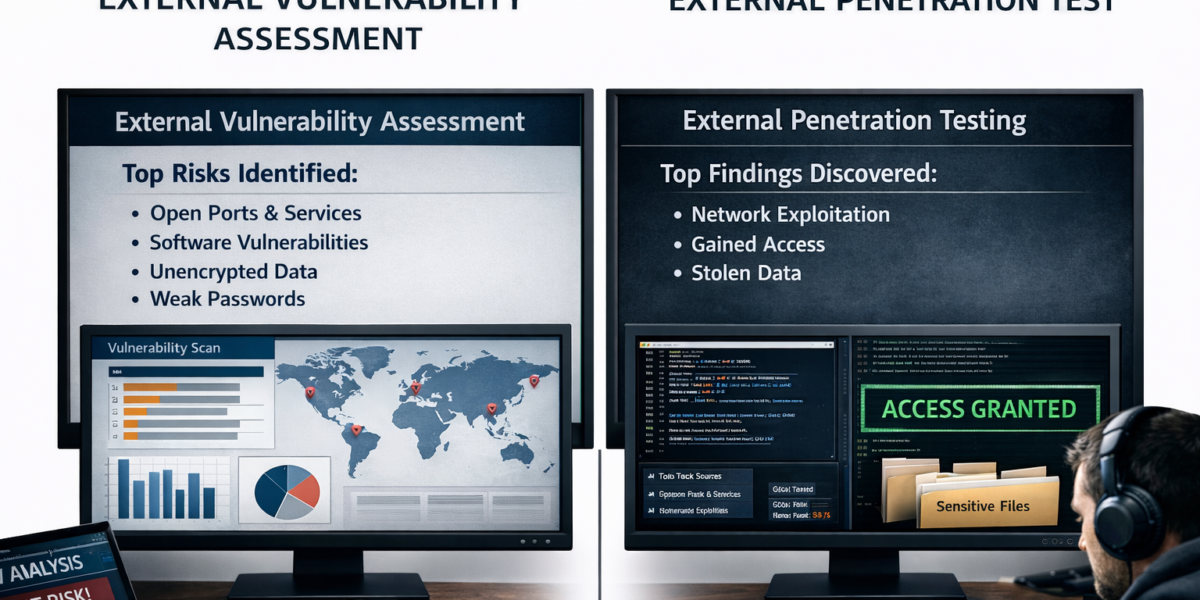
External penetration tests are a critical component of an organization’s cybersecurity strategy. They simulate real-world attacks by external hackers to identify vulnerabilities that could be exploited from outside the o...
How it’s Happening and Five Steps to Take to Protect Your Network When most people think of cutting edge cryptomining, they don’t think of using PLCs (Programmable Logic Controllers). Apparently criminal hackers and c...
With the business world in a massive state of upheaval, corporate security professionals need to revamp their strategies and tactics to reduce the risks of cyber attacks. To help them make these changes, I am sharing ...
Chief information security officers (CISOs) and information security officers (ISOs) within banking, credit union, healthcare and insurance companies should anticipate a new wave – and new types — of cyber attacks ...
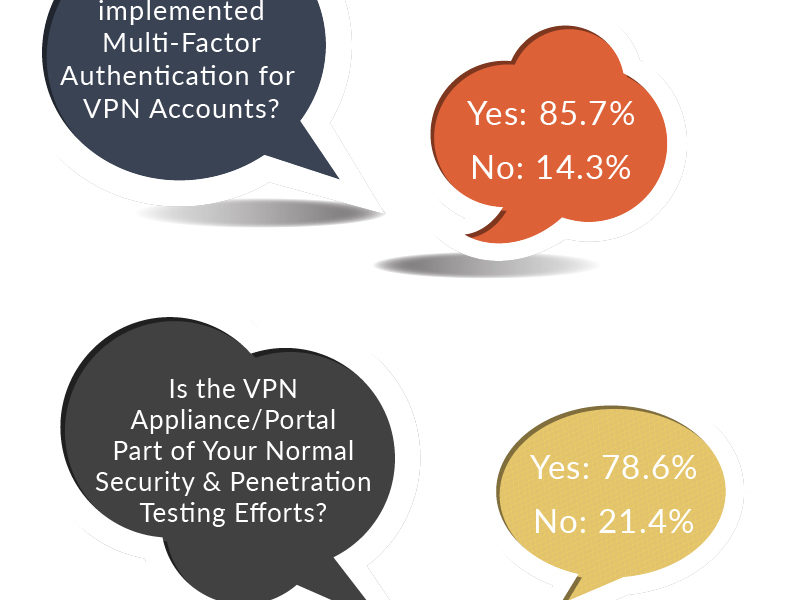
Focusing on Virtual Private Networks and Phishing Schemes Can Help Solve These Problems Your jobs as chief information officers (CISOs) were already tough. Then the pandemic hit. And your jobs got much mor...
NEWS RELEASE DATELINE: Charlotte, North Carolina FOR IMMEDIATE RELEASE: June 15, 2020 — Rebyc Security today introduces cyber security penetration testing services to help proactively address new and growing ...
Atrium Health Data Breach: What You Need to Know Atrium Health recently announced a breach potentially affecting more than 2.6 million patient records. Per the release, they stated that the breach occurred via a third pa...